Blogs
Decrypting email and documents from Office 365

Written by Steven Luke
Companies and people are moving to the cloud faster than ever before, and possibly with the leader in cloud business applications, Microsoft with its Office 365 suite of cloud applications. Some research suggests the Office 365 adoption rate reached close to 80% during 2020, and the speed of adoption is increasing especially among smaller businesses. There are many reasons companies choose to move to the cloud, but one of the main reasons is the flexibility Office 365 offers in securing customer data - including their emails and documents.
This data security, though it is a benefit for end users, can be a concern for organizations that need to collect user data for eDiscovery and investigative purposes. Office 365 users encrypt their emails at will, allowing only their recipients or shared users access to the contents of the files and emails. A company that needs to forensically collect their users’ data needs to find ways to work with Microsoft’s encryption so they can access the data they need without compromising their employees’ security. Nuix can help.
WHAT IS MICROSOFT PURVIEW INFORMATION PROTECTION?
Microsoft Purview Information Protection (formerly Microsoft Information Protection aka MIP), is a suite of protection tools provided to users of the Microsoft and Office 365 cloud products to secure their data. It comes at various levels depending on the enterprise subscription level, handling things like data loss prevention, content labeling, and most pertinent to this conversation: data encryption. In a previous iteration, the same product was called Azure Information Protection (AIP), and so it is common to hear both terms, MIP and AIP used in these discussions.
How Does MIP Encryption Work?
The encryption part of what MIP provides uses a technique called Azure RMS: Rights Management System. Below is a brief image demonstrating how it works:
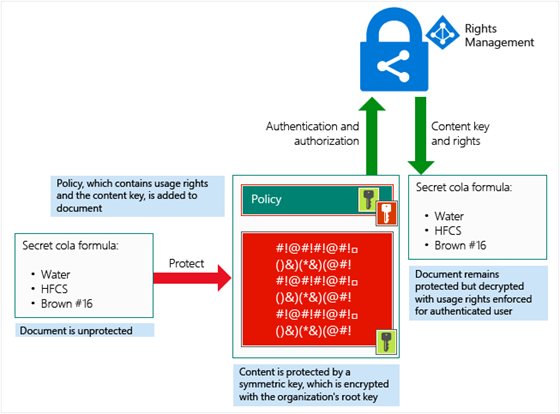
The content to be protected is embedded in a document and encrypted with a two-part key. The first part comes from the Azure Tenant - the domain to which the user’s Office 365 account is connected. The second part is a Rights Management Policy that defines who is allowed to read the contents. The encrypted content stays in the document, it is not sent to the server for encryption or decryption, instead, the policy is sent for authorization and if the reader is authorized, the application itself will do the decryption for the content reader. And that is where Nuix’s MIP Decryption Solution comes into play. This solution is authorized by the Azure tenant to do the decryption and so can decrypt the content and make it available in Nuix for eDiscovery and investigative purposes. For more details about how RMS technologies work, you can read about it here.
Why Is This A Problem?
Encryption and data protection are key requirements for cloud platforms, and the protection provided by Microsoft in this regard is a highly sought-after feature. It is user-friendly, helps organizations protect their data, and helps users protect themselves. So why is this a problem? Encryption is a double-edged sword. It protects the data from those that shouldn’t see it, but also blocks those with legitimate needs from seeing it well. As good stewards of data, we need to protect intellectual property from escaping the circles it needs to be in. We need to ensure when legal requirements arise, data can be discovered and investigated.
During mergers and acquisitions, we need to ensure data goes or stays with the entities it belongs to. In many industries, we need to ensure communications and activities meet various corporate, sector, or government compliance requirements. In short: to ensure proper governance of data there is a requirement that data is visible for legal, investigative, and compliance purposes. So, whereas encryption is a necessity to protect corporate and personal data, it must not do so in opposition to data governance. Nuix's MIP Decryption solution ensures that is the case.
How Do I Use Nuix To Decrypt Email And Documents On Office 365?
Nuix has implemented a MIP Decryption Solution that seamlessly works with your Azure Tenant’s authorization to decrypt user content. By working with Microsoft’s platform, it continues to offer the data protection MIP was designed for while giving those who need access the ability to read the content of encrypted emails and documents, search, link, find entities, and use all the other tools that Nuix software provides for data governance, IP protection, and compliance. Once decrypted, the information is available in Nuix’s suite of products.
Nuix MIP Decryption Features
Decrypt What You Want
Decrypt only the files you want to decrypt, and don’t waste time trying to decrypt files that aren’t encrypted, to begin with.
Working with RMS to decrypt items can be time-consuming - it requires round trips to the Microsoft servers to gain authorization for each item. It can be especially slow if you have large amounts of data and you start to reach throttling limits. With Nuix's MIP Decryption solution, you can reduce the time and number of network requests by limiting the items you send to be decrypted to just those items you need. This can significantly reduce the overall time of processing. To do this the solution will identify only the items that are encrypted, including:
• All encrypted Office documents (like Word, Excel, and PowerPoint)
• All email messages that contain encrypted “Restricted Permission Messages”
These items are presented to the user if they want to further filter what to work on.
Choose How Results Are Handled
The Nuix MIP Decryption solution can automatically replace the encrypted source material with the decrypted results. Alternatively, if the user wants to keep all the raw source material, they can append decrypted results as child items to the encrypted source to maintain access to everything right in the case.
Outcomes Clearly Indicated
It is important to know how the outcome of the decryption process on each item so you know if the data you need can be harvested. For this reason, items that go through the decryption process are tagged with their outcomes so their status is known and they can be easily found later.
User Feedback
The solution provides layers of feedback so the end user knows exactly what happened and why.
Complete Logging
Every step of the process is logged in detail. The logs are maintained in accessible areas and presented to the user when the process completes.
Failure Info
If an item can’t be decrypted for some reason the reason will be provided as an output of the process, attached to the item sent for decryption, and whenever possible the message will be meaningful and provide actionable information to make it easier for the user to choose what to do next.
Installation And Configuration Support
Part of what you get when you buy the Nuix MIP Protection Solution helps with configuring your Azure tenant and Purview environment and installation of the Solution itself. It can be tricky to get the user and application permissions just right and Nuix can provide the support needed to ensure it happens smoothly and quickly.
Application Support
Data integrity and security is a continually evolving field as companies like Microsoft must continuously adapt to varying cyber threats. Understandably, the tools they use to protect their users from such threats must evolve quickly. We will continue to support the utility to keep it up to date with the ever-changing data security landscape to minimize the downtime caused by sudden changes in protocols required by Microsoft.




![[SPANISH] TECNOLOGÍA, VERDAD Y CONFIANZA: ILUMINANDO LA IA ÉTICA](/sites/default/files/styles/portrait/public/2026-02/GettyImages-603195908%20%281%29_1.jpg.webp?itok=9hwLcF-n)
![[PORTUGESE] TECNOLOGIA, VERDADE E CONFIANÇA: ILUMINANDO A IA ÉTICA](/sites/default/files/styles/portrait/public/2026-02/GettyImages-603195908%20%281%29_0.jpg.webp?itok=Fvv5lSYe)