Nuix Neo
Data Privacy
UNDERSTAND WHAT DATA YOU HAVE, WHERE IT IS, AND HOW TO PROTECT IT WITH NUIX NEO DATA PRIVACY
Overview
Managing Data Privacy is now Faster, Easier and Smarter with Nuix NEO.
The Nuix Neo Data Privacy Solution stands at the intersection of privacy and power. Harnessing the speed and capabilities of the Nuix Neo platform, it delivers an unmatched balance of control, assurance and high-performance.
With its unparalleled capabilities and a uniquely powerful engine, Nuix Neo Data Privacy solution offers an easier, faster, and smarter approach to safeguarding sensitive information.
Use data to create value not risk
Our Data Privacy solution provides forensic depth and defensibility, empowering you to swiftly assess the value and risk of your data.
Gain valuable data intelligence to continually monitor and protect your business, meet compliance obligations, and ensure the utmost security for your customers.
Benefits
BENEFITS OF NUIX NEO DATA PRIVACY
IDENTIFY CONFIDENTIAL AND SENSITIVE DATA
Identify confidential and sensitive data such as PII and IP from connected and remote devices. Preview your data and determine if you need to move, or defensibly delete it.
UNCOVER, ORGANIZE, AND CATEGORIZE MASSIVE DATA VOLUMES
Drill into your data via automated searches to help you understand, catalogue, and categorize mass volumes of data across over 1,000 file formats, with unmatched speed and accuracy.
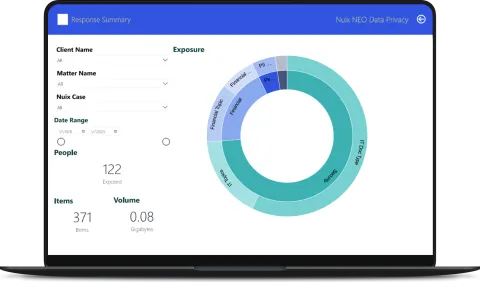
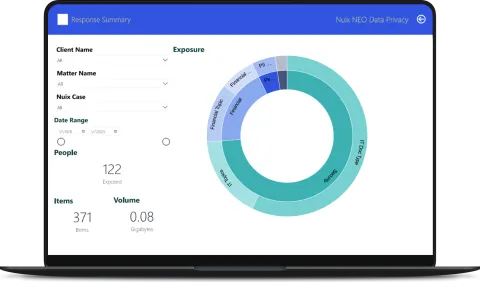
ANALYZE AND VISUALIZE YOUR DATA
Analyze and visualize your data via sophisticated workflow management systems, enabling you to make more accurate and informed decisions.
ACT SWIFTLY AND MORE CONFIDENTLY
Act swiftly and more confidently knowing you are armed with comprehensive information about your data and its attributes, that's supported by sophisticated AI analytics, and backed by our world-renowned proprietary data interrogation techniques.
Features

Reduce your risk profile
Take control of your data and reduce risk with Nuix Neo Data Privacy. Powered by explainable AI, it identifies and deduplicates sensitive data, making it easy to manage compliance while minimizing unnecessary exposure. Visual tools and automated workflows provide clarity and efficiency in navigating data challenges.

get AUTOMATED INSIGHTS
Unlock the power of intelligent automation with advanced automated insights enable you to quickly identify sensitive data, such as PII and confidential information, across massive data volumes with unmatched accuracy. By streamlining discovery and classification processes, maintain regulatory compliance while saving valuable time and resources.
What's new in nuix neo? Make working with your data even faster, smarter, and easier.
Advantages
ADVANTAGES OF NUIX NEO DATA PRIVACY
For over 20 years, Nuix has been helping organizations make sense of their data. It is that experience that underpins our solution for data privacy and puts you in control of your data.
💠See value sooner
Purposefully designed to help organizations manage their data privacy, your Nuix Neo Data Privacy solution can be implemented quickly, seamlessly, and with minimal configuration so you can get back to business and realize its true value sooner.
💠Streamlined user interface
Increase productivity with single sign-on access and a completely modern and integrated interface that is intuitive and efficient to use.
💠Get to the answers quicker
With a cognitive interface engine, pre-trained with specific models for detecting data privacy information, our explainable and defensible AI can help identify patterns and correlations that no human can find, so you can find what you need, isolate valuable or risky information, while by passing unimportant data, more quickly and accurately.
💠Automate processes
Work faster and smarter by leveraging the power of AI to automate repetitive tasks, prioritize data risks so you spend less time filtering through huge data volumes, and focus on finding what you need.
💠Deploy it your way
Depending on your business requirements, we can support hyperscale, in the cloud, on-premise or partner supported deployment.
Please set a case study or resource
Use Cases
Nuix Neo Data Privacy Use Cases
There are a number of use cases across a range of industries and verticals that Nuix Neo can help with. See how.
Data Breach Notifications
Data breaches are an unfortunate reality of business today. Swiftly pinpoint compromised data, meet regulatory compliance standards, and complete data breach notifications faster, easier, and smarter, with Nuix Neo Data Privacy solution.
Data Breach Readiness
No organization, industry or individual is immune to a data breach. Nuix Neo Data Privacy solution's advanced data discovery and classification capabilities give organizations comprehensive visibility into their data landscape.
Managing Information Access Requests
An explosion of information requests and strict regulations pressure organizations to stay compliant and meet public expectations. Fast track responses with Nuix Neo Data Privacy’s advanced data discovery, classification, and redaction capabilities.
PINPOINT PERSONALLY IDENTIFIABLE INFORMATION
With Nuix Neo Data Privacy solution organizations can pinpoint PII and gain a full understand of their data landscape. Take control: identify, redact, and deduplicate PII to reduce your risk profile and stay compliant.
Fact Sheets
Nuix Neo Data Privacy for Data Breach Readiness
With Nuix Neo Data Privacy, organizations have a comprehensive way to understand their data landscape, enabling them to proactively identify sensitive or at-risk data and take measures to safeguard it. Adhere to strict regulatory requirements, avoid hefty fines, and minimize the impact of a data breach today. Reducing your risk profile is faster, easier, and smarter with Nuix Neo Data Privacy.
Speak to an expert or request a demo TODAY
See for yourself how our innovative software can transform your data into actionable intelligence and help answer your biggest data challenges.
If your browser is experiencing any issues with the form on this page, click here to open it in a new window.
















![[SPANISH] TECNOLOGÍA, VERDAD Y CONFIANZA: ILUMINANDO LA IA ÉTICA](/sites/default/files/styles/portrait/public/2026-02/GettyImages-603195908%20%281%29_1.jpg.webp?itok=9hwLcF-n)
![[PORTUGESE] TECNOLOGIA, VERDADE E CONFIANÇA: ILUMINANDO A IA ÉTICA](/sites/default/files/styles/portrait/public/2026-02/GettyImages-603195908%20%281%29_0.jpg.webp?itok=Fvv5lSYe)