Resource Hub
Resources
Discover the latest Nuix whitepapers, fact-sheets, whitepapers and webinars
Blogs
Blogs

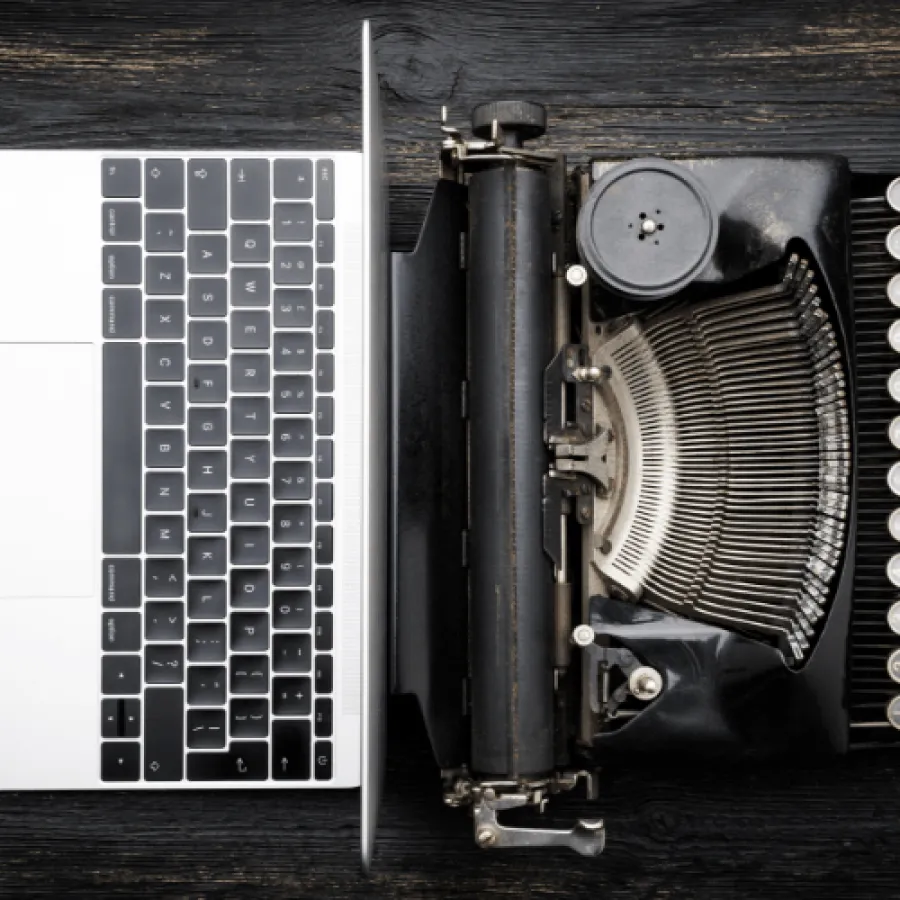
Xplore_AI: What’s in a name? Be specific!
Read more ›
Nuix Notes: Monthly updates from the CEO - Jul24
Read more ›
Xplore_AI: A Matter of Trust
Read more ›
Nuix Notes: Monthly updates from the CEO - Jun24
Read more ›
Xplore_AI: Into the Breach!
Read more ›
Nuix Notes: Monthly updates from the CEO - May24
Read more ›
Xplore_AI: Water, water everywhere
Read more ›
Nuix Notes: Monthly updates from the CEO - Feb24
Read more ›
White Papers
White Papers
Fact Sheets
Fact Sheets
Videos
Videos
Use Case
Use Case
Brochures
Brochures
Podcasts
Podcasts
Frequently asked questions
Our fiscal year runs from 1 July to 30 June.
Our ASX code is NXL.
Our auditors are KPMG.
A copy of the Annual Report can be downloaded from the Annual Reports section in the Investor Centre











































































![[German] Das Ermittlungs-Paradox: Datenflut Durch Neue Technologien Stellt Ermittlungen Vor Herausforderungen](/sites/default/files/styles/portrait/public/2026-02/Screenshot%202026-02-09%20at%2011.17.35%E2%80%AFAM_0_2.png.webp?itok=qpDD5-Zf)
![[SPANISH] LA PARADOJA DE LA INVESTIGACIÓN: LOS AVANCES TECNOLÓGICOS GENERAN UN ALUVIÓN DE DATOS QUE AHOGA LAS INVESTIGACIONES](/sites/default/files/styles/portrait/public/2026-02/Screenshot%202026-02-09%20at%2011.17.35%E2%80%AFAM_0_1.png.webp?itok=nYMlccG2)
![[PORTUGESE] O PARADOXO DA INVESTIGAÇÃO: AVANÇOS TECNOLÓGICOS GERAM UM DILÚVIO DE DADOS QUE SOBRECARREGA AS INVESTIGAÇÕES](/sites/default/files/styles/portrait/public/2026-02/Screenshot%202026-02-09%20at%2011.17.35%E2%80%AFAM_0_0.png.webp?itok=sI_dO_yg)



![[SPANISH] TECNOLOGÍA, VERDAD Y CONFIANZA: ILUMINANDO LA IA ÉTICA](/sites/default/files/styles/portrait/public/2026-02/GettyImages-603195908%20%281%29_1.jpg.webp?itok=9hwLcF-n)
![[PORTUGESE] TECNOLOGIA, VERDADE E CONFIANÇA: ILUMINANDO A IA ÉTICA](/sites/default/files/styles/portrait/public/2026-02/GettyImages-603195908%20%281%29_0.jpg.webp?itok=Fvv5lSYe)